Documentation Index
Fetch the complete documentation index at: https://developers.authlete.com/llms.txt
Use this file to discover all available pages before exploring further.
For Authlete 2.x documentation, see 2.x version.
Client Authentication Using the tls_client_auth Method
Preface
A section of RFC 8705, “2. Mutual TLS for OAuth Client Authentication” defines how authorization servers authenticate clients using mutual TLS. Authlete offers a feature that enables authorization servers to authenticate clients using TLS client certificates. This article describes an overview of the feature and instructions to enable it.How TLS Client Authentication Works in Authlete
The TLS client authentication feature of Authlete employsclient ID and subject name (subject distinguished name / subject alternative name) to authenticate clients.
When processing token requests, an authorization server is responsible for providing the client ID and subject name properties to Authlete. Client ID is included in content of a token request by a client, so an authorization server doesn’t have to care. “Subject name” is not in the content but in a client certificate, that can be obtained from a mutual TLS connection between a client and an authorization server.
On Authlete’s side, you have to enable TLS_CLIENT_AUTH client authentication method and register the client’s subject name. 
Service settings
| Tab | Item | Value |
|---|---|---|
| Service Settings > Endpoints > Token | Supported Client Authentication Methods | TLS_CLIENT_AUTH |
- Log in to the Authlete Management Console.
- Click on your Organization name and choose your Service.
- Navigate to Service Settings > Endpoints > Token > General
- Under
Client Authentication Method, select theTLS_CLIENT_AUTHmethod. - Click Save Changes to update your service settings.

Client settings
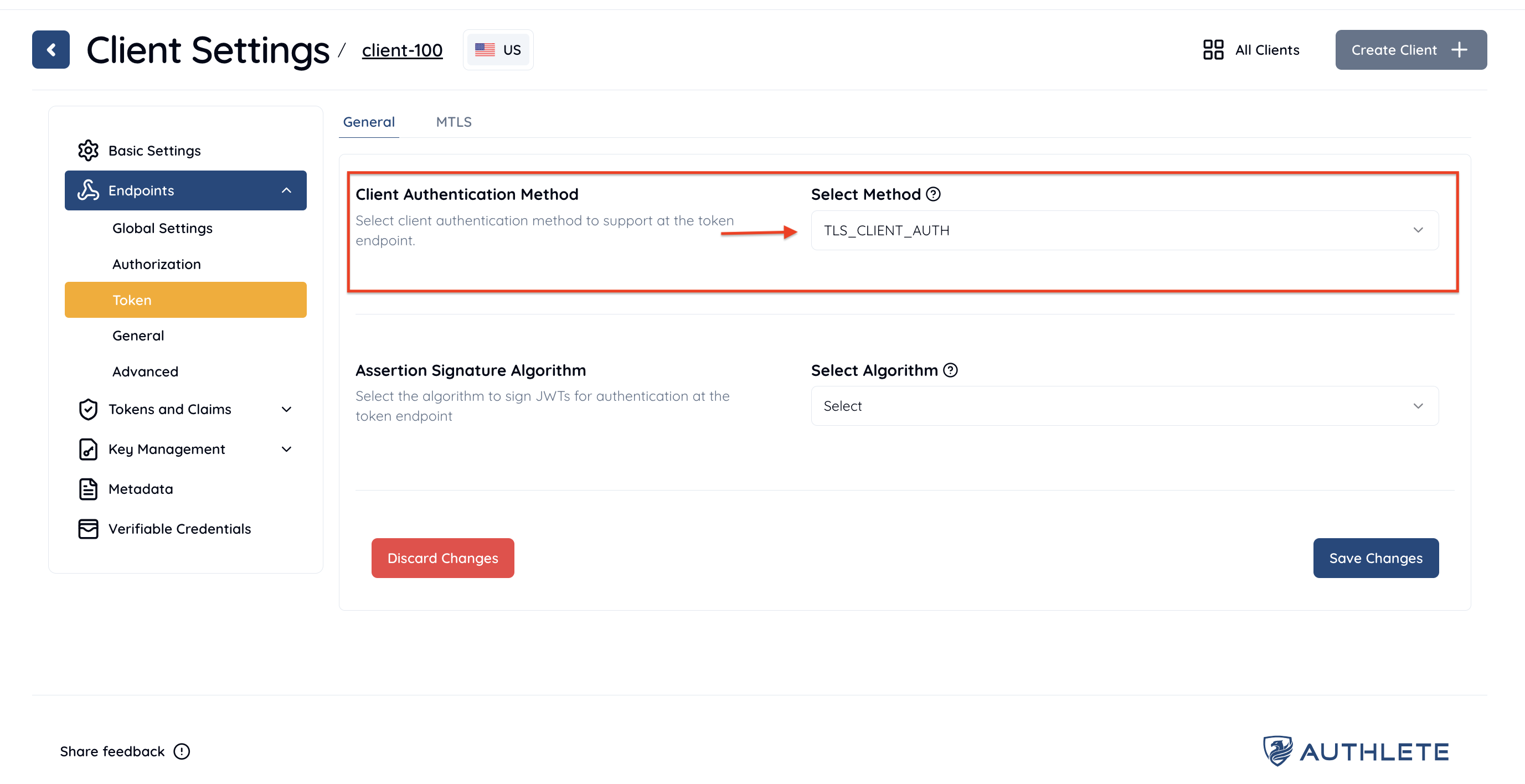
This example uses Subject Distinguished Name (Subject DN) as a type of “subject name” though, Authlete in fact supports other various types of Subject Alternative Name (SAN) in addition to Subject DN.To enable the
Tab Item Value Client Settings > Endpoints > Token Client Authentication Method TLS_CLIENT_AUTH Client Settings > Endpoints > Token Subject Distinguished Name (e.g. CN=client.example.org, O=Client, L=Chiyoda-ku, ST=Tokyo, C=JP)
TLS_CLIENT_AUTH method for your client:
- Log in to the Authlete Management Console.
- Click on your Organization name and choose your Service.
- Navigate to Client Settings > Endpoints > Token > General
- Under
Client Authentication Method, open the dropdown menu and select theTLS_CLIENT_AUTHmethod. - Click Save Changes to apply the updates.
 To register the
To register the subject name for your client:
- Navigate to Client Settings > Endpoints > Token > MTLS
-
Enter a desired value for
Subject Distinguished Name. You can also specify other name values used for client authentication, including:- Subject Alternative Name DNS
- Subject Alternative Name IP Address
- Subject Alternative Name URI
- Subject Alternative Name Email
- Self Signed Certificate Key ID
- Click Save Changes to apply the updates.
 With the settings above, Authlete will support mutual TLS authentication as a client authentication method and apply the method to process token requests from the client above. Subject DN CN=client.example.org, … is used as the identifier of the client.
With the settings above, Authlete will support mutual TLS authentication as a client authentication method and apply the method to process token requests from the client above. Subject DN CN=client.example.org, … is used as the identifier of the client.
Example
The following is an example of a request to /auth/token (folded for readability). An authorization server establishes a mutual TLS connection with a client, obtains the client’s certificate from the connection, and makes the request to the API. Content of a token request, that includes a client ID (client_id), is specified as a value of “parameters,” and a client certificate as a value of “clientCertificate”.See Also
This article describes basics of client authentication configuration in Authlete.
This article describes setup instructions for Authlete to use “Mutual-TLS certificate-bound access tokens,” defined in “RFC 8705 OAuth 2.0 Mutual-TLS Client Authentication and Certificate-Bound Access Tokens.”
This video is one of the sessions at “Financial APIs Workshop 2018 ”, held on July 24th, 2018 in Tokyo. Justin Richer from Authlete talks about comparison of Authlete’s unique semi-hosted approach and traditional approaches for deploying OAuth infrastructure, and how Authlete has extended its client authentication functions and supported mutual TLS to implement Financial-grade API (FAPI).