Documentation Index
Fetch the complete documentation index at: https://developers.authlete.com/llms.txt
Use this file to discover all available pages before exploring further.
What is Authlete?
Authlete is a BaaS (Backend as a Service) for implementing OAuth 2.0 and OpenID Connect. By using the Web APIs that Authlete provides, you can implement OAuth 2.0 and OpenID Connect functionality with less effort.Why do you need Authlete?
When you implement a Web API, you need to implement OAuth 2.0 (and OpenID Connect) on the service provider side. That implementation is not trivial and often requires significant resources and time. Managing personal data also demands great care. Using limited engineering resources to address these challenges while launching before competitors is difficult. Authlete helps you address these challenges. Authlete supports many finalized and draft API authorization-related specifications. Using Authlete makes it relatively easy to implement a Web API.Authlete features
Because Authlete provides APIs to build an authorization server rather than a prebuilt server, it offers the following benefits.Use your preferred languages and frameworks and shorten development time
Use your preferred languages and frameworks and shorten development time
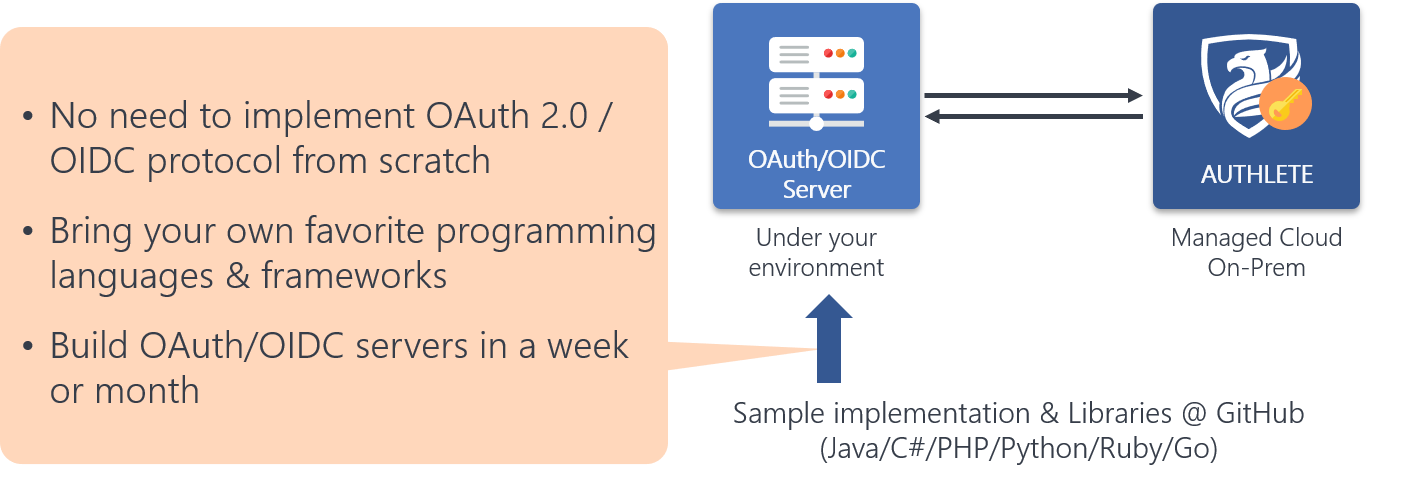
What distinguishes Authlete is that all functionality required to implement an OAuth 2.0 and OpenID Connect server is designed and implemented as Web APIs. Not only client application registration and authorization server metadata management, but also the logic behind authorization and token endpoints is provided via Web APIs.
As a result, you can use Authlete with any language or framework—Java, Ruby, PHP, C#, and more. Using OSS libraries, you can implement a server in days to weeks.
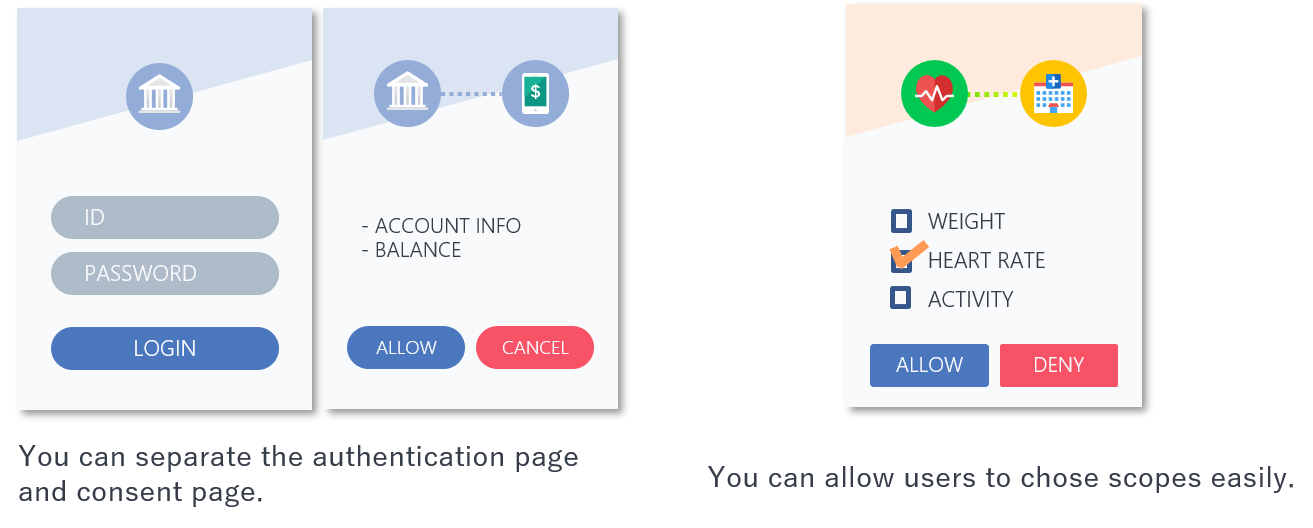
Design consent UI and flows your way
Design consent UI and flows your way
Authlete delivers OAuth/OIDC behavior through Web APIs. The authorization and token endpoints run in your environment. So you can design the consent UI and user flow to match your product and brand.
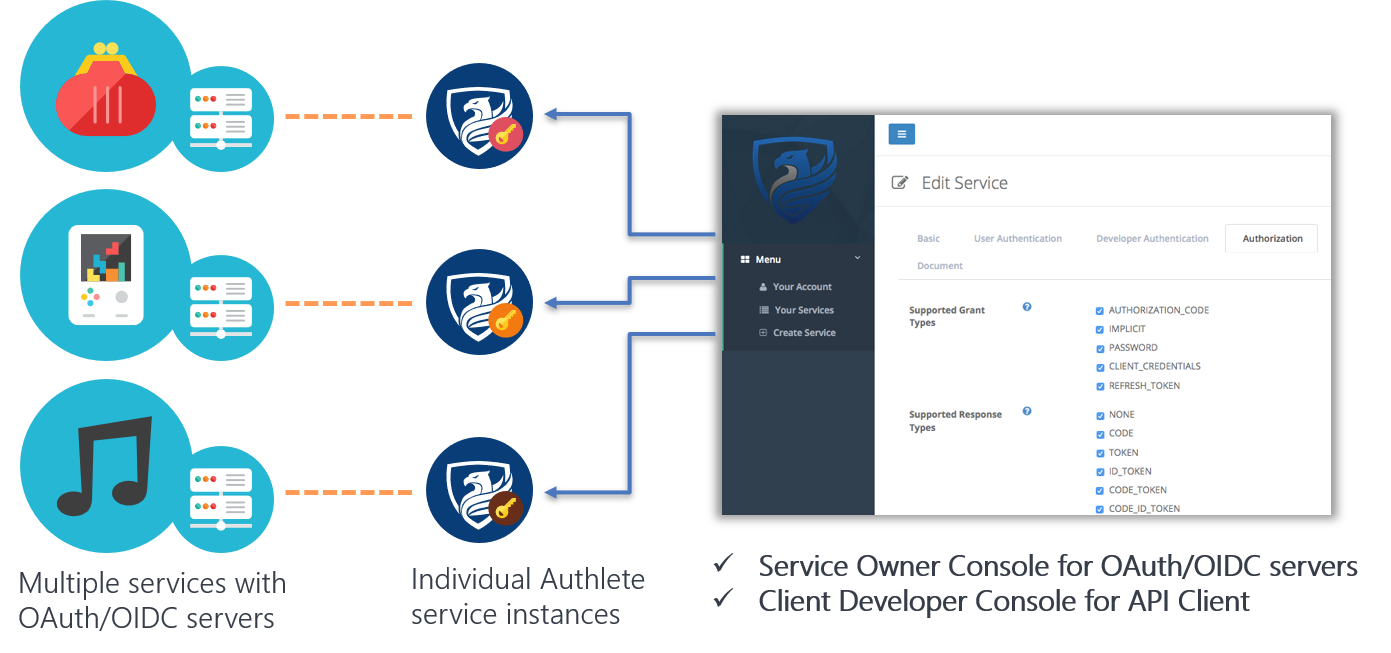
Run and manage multiple authorization servers and API clients with one Authlete account
Run and manage multiple authorization servers and API clients with one Authlete account
Use any identity, authentication, session, API management, or fraud-detection solution
Use any identity, authentication, session, API management, or fraud-detection solution
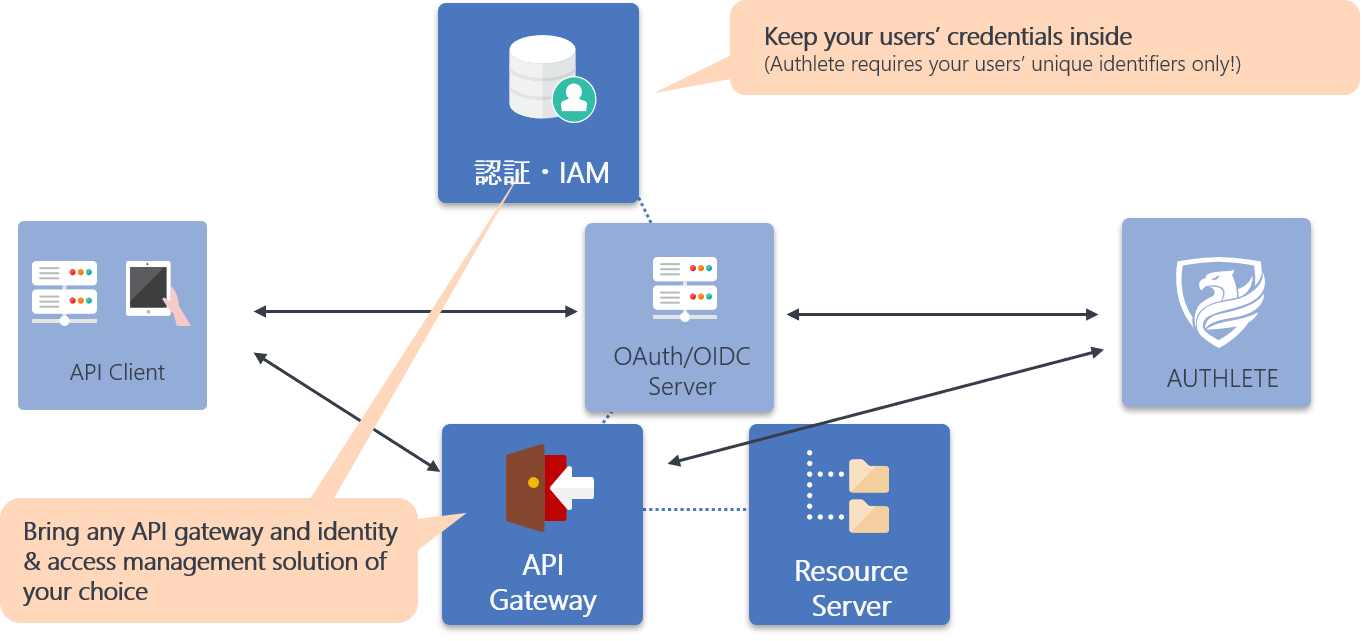
Authlete focuses on authorization and works with any user authentication, identity, or API management solution. You can keep your existing authentication and identity infrastructure and add OAuth/OIDC with minimal development.
Keep end-user personal data in your own systems
Keep end-user personal data in your own systems
When you use Authlete, the only end-user information you need to pass to Authlete is a stable subject identifier per user. Authlete accepts that identifier and associates it with tokens and other protocol data.
You do not need to share end-user names, email addresses, or credentials with Authlete. This is a major difference from all-in-one authentication-and-authorization solutions.
When generating ID tokens, you can send the claims to embed to Authlete’s API to fulfill OpenID Connect behavior.
Use the latest OAuth and OpenID Connect specifications
Use the latest OAuth and OpenID Connect specifications
Authlete supports RFC 6749 and many other specifications. It is OpenID Connect certified and was the first production-ready solution to achieve Financial-grade API (FAPI) certification.
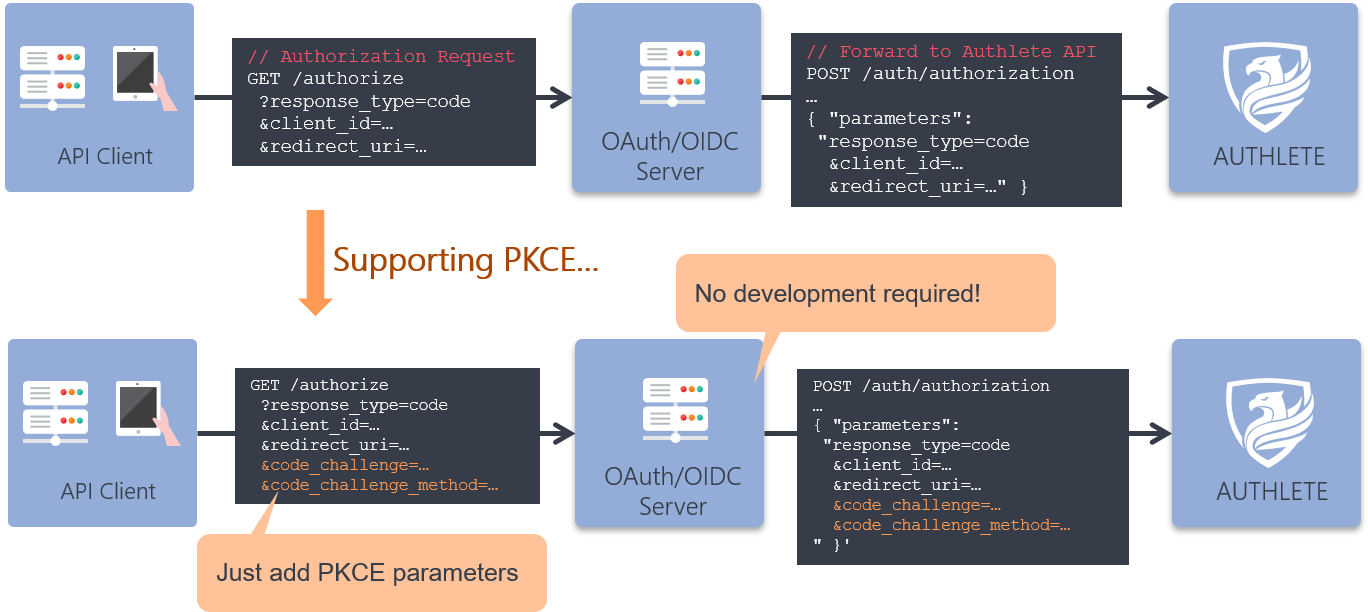
Because OAuth/OIDC behavior is delivered via Web APIs, supporting new specifications places minimal burden on your code. For example, to support PKCE you only need to add the relevant parameters from the client; no change is required in your authorization server implementation.
Below is a subset of the specifications Authlete currently supports (some features are available on Enterprise plans only).